Wpa2 Hash Crack
Posted in:admin
Being a penetration tester makes us feel like a group of traveler. Discovering the internal world of the institution during engagement gives us the opportunity to. Last year, I wrote an article covering popular wireless hacking tools to crack or recover password of wireless network. We added 13 tools in that article which were. John is able to crack WPAPSK and WPA2PSK passwords. Recent changes have improved performance when there are multiple hashes in the input file, that have the same. Wpa2 Hash Crack' title='Wpa2 Hash Crack' />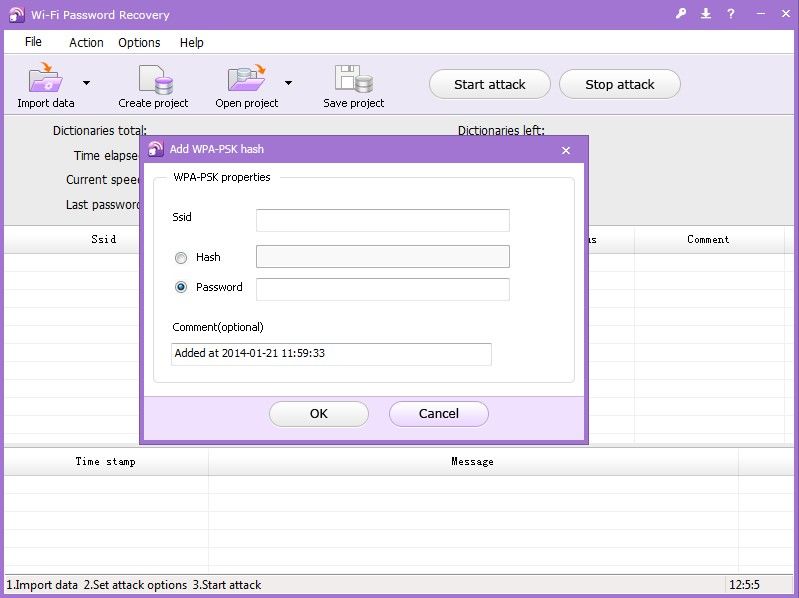 GPUHASH. WPAWPA2 hash cracker. I just wanted to thank you guys for the support youve given me today. Adam. Most of you lot would be aware what WPAWPA2 is so I wont bang on about the encryption or protocols a great deal. In short WPA and WPA2 both have a maximum of 256bit. WiFi Password Recovery is ideal wireless network security monitor that help you do network security detection. This WiFi protector helps you recover forgotten or. All uncracked hashes are added to the crackqueue. Click here to see the status of your previously submitted hash. Funktionsweise. WPA enthlt die Architektur von WEP, bringt jedoch zustzlichen Schutz durch dynamische Schlssel, die auf dem Temporal Key Integrity Protocol. Worlds fastest md5crypt, phpass, mscash2 and WPA WPA2 cracker Worlds first and only GPGPU based rule engine Free MultiGPU up to 128 gpus MultiHash up to 15. WPA2-WiFi-password-using-reaver-1.jpg?resize=872%2C270' alt='Wpa2 Hash Crack' title='Wpa2 Hash Crack' />Popular Tools for Brute force Attacks Updated for 2. New SQL Injection Lab Skillset Labs walk you through infosec tutorials, step by step, with over 3. FREE FREE SQL Injection Labs. The brute force attack is still one of the most popular password cracking methods. Nevertheless, it is not just for password cracking. Brute force attacks can also be used to discover hidden pages and content in a web application. Wpa2 Hash Crack' title='Wpa2 Hash Crack' />This attack is basically a hit and try until you succeed. This attack sometimes takes longer, but its success rate is higher. In this article, I will try to explain brute force attacks and popular tools used in different scenarios for performing brute force attack to get desired results. What is a Brute force attack Brute force attack when an attacker uses a set of predefined values to attack a target and analyze the response until he succeeds. Success depends on the set of predefined values. LALnzc/UvdXM3fIChI/AAAAAAAABDM/Qf6-WSmZ3Mc/s1600/hashcat14.png' alt='Wpa2 Hash Crack' title='Wpa2 Hash Crack' />If it is larger, it will take more time, but there is better probability of success. The most common and easiest to understand example of the brute force attack is the dictionary attack to crack the password. In this, attacker uses a password dictionary that contains millions of words that can be used as a password. Then the attacker tries these passwords one by one for authentication. If this dictionary contains the correct password, attacker will succeed. In traditional brute force attack, attacker just tries the combination of letters and numbers to generate password sequentially. However, this traditional technique will take longer when the password is long enough. These attacks can take several minutes to several hours or several years depending on the system used and length of password. To prevent password cracking by using a brute force attack, one should always use long and complex passwords. This makes it hard for attacker to guess the password, and brute force attacks will take too much time. Most of the time, Word. Press users face brute force attacks against their websites. Account lock out is another way to prevent the attacker from performing brute force attacks on web applications. However, for offline software, things are not as easy to secure. Similarly, for discovering hidden pages, the attacker tries to guess the name of the page, sends requests, and sees the response. If the page does not exist, it will show response 4. In this way, it can find hidden pages on any website. Brute force is also used to crack the hash and guess a password from a given hash. In this, the hash is generated from random passwords and then this hash is matched with a target hash until the attacker finds the correct one. Therefore, the higher the type of encryption 6. Reverse brute force attack. A reverse brute force attack is another term that is associated with password cracking. It takes a reverse approach in password cracking. In this, attacker tries one password against multiple usernames. Think if you know a password but do not have any idea of the usernames. In this case, you can try the same password and guess the different user names until you find the working combination. Now, you know that Brute forcing attack is mainly used for password cracking. You can use it in any software, any website or any protocol, which do not block requests after few invalid trials. In this post, I am going to add few brute force password cracking tools for different protocols. Popular tools for brute force attacks. Aircrack ng. I am sure you already know about Aircrack ng tool. This is a popular wireless password cracking tool available for free. I also mentioned this tool in our older post on most popular password cracking tools. This tool comes with WEPWPAWPA2 PSK cracker and analysis tools to perform attack on WIFi 8. Aircrack NG can be used for any NIC, which supports raw monitoring mode. It basically performs dictionary attacks against a wireless network to guess the password. As you already know, success of the attack depends on the dictionary of passwords. The better and effective the password dictionary is the more likely it is that it will crack the password. It is available for Windows and Linux platforms. It has also been ported to run on i. OS and Android platforms. You can try on given platforms to see how this tool works. Download Aircrack ng from this link http www. John the Ripper. John the Ripper is another awesome tool that does not need any introduction. It has been a favorite choice for performing brute force attack for long time. This free password cracking software was initially developed for Unix systems. Later, developers released it for various other platforms. Now, it supports fifteen different platforms including Unix, Windows, DOS, Be. OS, and Open. VMS. You can use this either to identify weak passwords or to crack passwords for breaking authentication. This tool is very popular and combines various password cracking features. It can automatically detect the type of hashing used in a password. Therefore, you can also run it against encrypted password storage. Basically, it can perform brute force attack with all possible passwords by combining text and numbers. However, you can also use it with a dictionary of passwords to perform dictionary attacks. Download John the Ripper from this link http www. Rainbow Crack. Rainbow Crack is also a popular brute forcing tool used for password cracking. It generates rainbow tables for using while performing the attack. In this way, it is different from other conventional brute forcing tools. Rainbow tables are pre computed. It helps in reducing the time in performing the attack. The good thing is that there are various organizations, which already published the pre computer rainbow tables for all Internet users. Game Bred Apbt Kennel more. To save time, you can download those rainbow tables and use in your attacks. This tool is still in active development. It is available for both Windows and Linux and supports all latest versions of these platforms. Download Rainbow Crack and read more about this tool from this link http project rainbowcrack. Ethical Hacking Training Resources Info. SecCain and Abel. I am sure you have already heard the name of this password cracking tool. It can help in cracking various kind of passwords by performing brute forcing attacks, dictionary attacks, and cryptanalysis attacks. Cryptanalysis attacks are done by using the rainbow tables as mentioned in the previous tool. It is worth to mention that some virus scanners detect it as malware. Avast and Microsoft Security Essentials report it as malware and block it in system. If it is in your system, you should first block your antivirus. Its basic functions Sniffing the network. Cracking encrypted passwords using Dictionary. Brute Force and Cryptanalysis attacks. Recording Vo. IP conversations. Decoding scrambled passwords. Recovering wireless network keys. Revealing password boxes. Uncovering cached passwords. Analyzing routing protocols. The latest version of the tool has many features, and has added sniffing to perform Man in the Middle attacks. Download Cain and Able from this link http www. L0pht. Crack. L0pht. Crack is known for its ability to crack Windows passwords. It uses dictionary, brute force, hybrid attacks, and rainbow tables. The most notable features of l. Windows versions, multiprocessor algorithms, and networks monitoring and decoding. If you want to crack the password of Windows system, you can try this tool. Download L0pht. Crack from this link http www.
GPUHASH. WPAWPA2 hash cracker. I just wanted to thank you guys for the support youve given me today. Adam. Most of you lot would be aware what WPAWPA2 is so I wont bang on about the encryption or protocols a great deal. In short WPA and WPA2 both have a maximum of 256bit. WiFi Password Recovery is ideal wireless network security monitor that help you do network security detection. This WiFi protector helps you recover forgotten or. All uncracked hashes are added to the crackqueue. Click here to see the status of your previously submitted hash. Funktionsweise. WPA enthlt die Architektur von WEP, bringt jedoch zustzlichen Schutz durch dynamische Schlssel, die auf dem Temporal Key Integrity Protocol. Worlds fastest md5crypt, phpass, mscash2 and WPA WPA2 cracker Worlds first and only GPGPU based rule engine Free MultiGPU up to 128 gpus MultiHash up to 15. WPA2-WiFi-password-using-reaver-1.jpg?resize=872%2C270' alt='Wpa2 Hash Crack' title='Wpa2 Hash Crack' />Popular Tools for Brute force Attacks Updated for 2. New SQL Injection Lab Skillset Labs walk you through infosec tutorials, step by step, with over 3. FREE FREE SQL Injection Labs. The brute force attack is still one of the most popular password cracking methods. Nevertheless, it is not just for password cracking. Brute force attacks can also be used to discover hidden pages and content in a web application. Wpa2 Hash Crack' title='Wpa2 Hash Crack' />This attack is basically a hit and try until you succeed. This attack sometimes takes longer, but its success rate is higher. In this article, I will try to explain brute force attacks and popular tools used in different scenarios for performing brute force attack to get desired results. What is a Brute force attack Brute force attack when an attacker uses a set of predefined values to attack a target and analyze the response until he succeeds. Success depends on the set of predefined values. LALnzc/UvdXM3fIChI/AAAAAAAABDM/Qf6-WSmZ3Mc/s1600/hashcat14.png' alt='Wpa2 Hash Crack' title='Wpa2 Hash Crack' />If it is larger, it will take more time, but there is better probability of success. The most common and easiest to understand example of the brute force attack is the dictionary attack to crack the password. In this, attacker uses a password dictionary that contains millions of words that can be used as a password. Then the attacker tries these passwords one by one for authentication. If this dictionary contains the correct password, attacker will succeed. In traditional brute force attack, attacker just tries the combination of letters and numbers to generate password sequentially. However, this traditional technique will take longer when the password is long enough. These attacks can take several minutes to several hours or several years depending on the system used and length of password. To prevent password cracking by using a brute force attack, one should always use long and complex passwords. This makes it hard for attacker to guess the password, and brute force attacks will take too much time. Most of the time, Word. Press users face brute force attacks against their websites. Account lock out is another way to prevent the attacker from performing brute force attacks on web applications. However, for offline software, things are not as easy to secure. Similarly, for discovering hidden pages, the attacker tries to guess the name of the page, sends requests, and sees the response. If the page does not exist, it will show response 4. In this way, it can find hidden pages on any website. Brute force is also used to crack the hash and guess a password from a given hash. In this, the hash is generated from random passwords and then this hash is matched with a target hash until the attacker finds the correct one. Therefore, the higher the type of encryption 6. Reverse brute force attack. A reverse brute force attack is another term that is associated with password cracking. It takes a reverse approach in password cracking. In this, attacker tries one password against multiple usernames. Think if you know a password but do not have any idea of the usernames. In this case, you can try the same password and guess the different user names until you find the working combination. Now, you know that Brute forcing attack is mainly used for password cracking. You can use it in any software, any website or any protocol, which do not block requests after few invalid trials. In this post, I am going to add few brute force password cracking tools for different protocols. Popular tools for brute force attacks. Aircrack ng. I am sure you already know about Aircrack ng tool. This is a popular wireless password cracking tool available for free. I also mentioned this tool in our older post on most popular password cracking tools. This tool comes with WEPWPAWPA2 PSK cracker and analysis tools to perform attack on WIFi 8. Aircrack NG can be used for any NIC, which supports raw monitoring mode. It basically performs dictionary attacks against a wireless network to guess the password. As you already know, success of the attack depends on the dictionary of passwords. The better and effective the password dictionary is the more likely it is that it will crack the password. It is available for Windows and Linux platforms. It has also been ported to run on i. OS and Android platforms. You can try on given platforms to see how this tool works. Download Aircrack ng from this link http www. John the Ripper. John the Ripper is another awesome tool that does not need any introduction. It has been a favorite choice for performing brute force attack for long time. This free password cracking software was initially developed for Unix systems. Later, developers released it for various other platforms. Now, it supports fifteen different platforms including Unix, Windows, DOS, Be. OS, and Open. VMS. You can use this either to identify weak passwords or to crack passwords for breaking authentication. This tool is very popular and combines various password cracking features. It can automatically detect the type of hashing used in a password. Therefore, you can also run it against encrypted password storage. Basically, it can perform brute force attack with all possible passwords by combining text and numbers. However, you can also use it with a dictionary of passwords to perform dictionary attacks. Download John the Ripper from this link http www. Rainbow Crack. Rainbow Crack is also a popular brute forcing tool used for password cracking. It generates rainbow tables for using while performing the attack. In this way, it is different from other conventional brute forcing tools. Rainbow tables are pre computed. It helps in reducing the time in performing the attack. The good thing is that there are various organizations, which already published the pre computer rainbow tables for all Internet users. Game Bred Apbt Kennel more. To save time, you can download those rainbow tables and use in your attacks. This tool is still in active development. It is available for both Windows and Linux and supports all latest versions of these platforms. Download Rainbow Crack and read more about this tool from this link http project rainbowcrack. Ethical Hacking Training Resources Info. SecCain and Abel. I am sure you have already heard the name of this password cracking tool. It can help in cracking various kind of passwords by performing brute forcing attacks, dictionary attacks, and cryptanalysis attacks. Cryptanalysis attacks are done by using the rainbow tables as mentioned in the previous tool. It is worth to mention that some virus scanners detect it as malware. Avast and Microsoft Security Essentials report it as malware and block it in system. If it is in your system, you should first block your antivirus. Its basic functions Sniffing the network. Cracking encrypted passwords using Dictionary. Brute Force and Cryptanalysis attacks. Recording Vo. IP conversations. Decoding scrambled passwords. Recovering wireless network keys. Revealing password boxes. Uncovering cached passwords. Analyzing routing protocols. The latest version of the tool has many features, and has added sniffing to perform Man in the Middle attacks. Download Cain and Able from this link http www. L0pht. Crack. L0pht. Crack is known for its ability to crack Windows passwords. It uses dictionary, brute force, hybrid attacks, and rainbow tables. The most notable features of l. Windows versions, multiprocessor algorithms, and networks monitoring and decoding. If you want to crack the password of Windows system, you can try this tool. Download L0pht. Crack from this link http www.